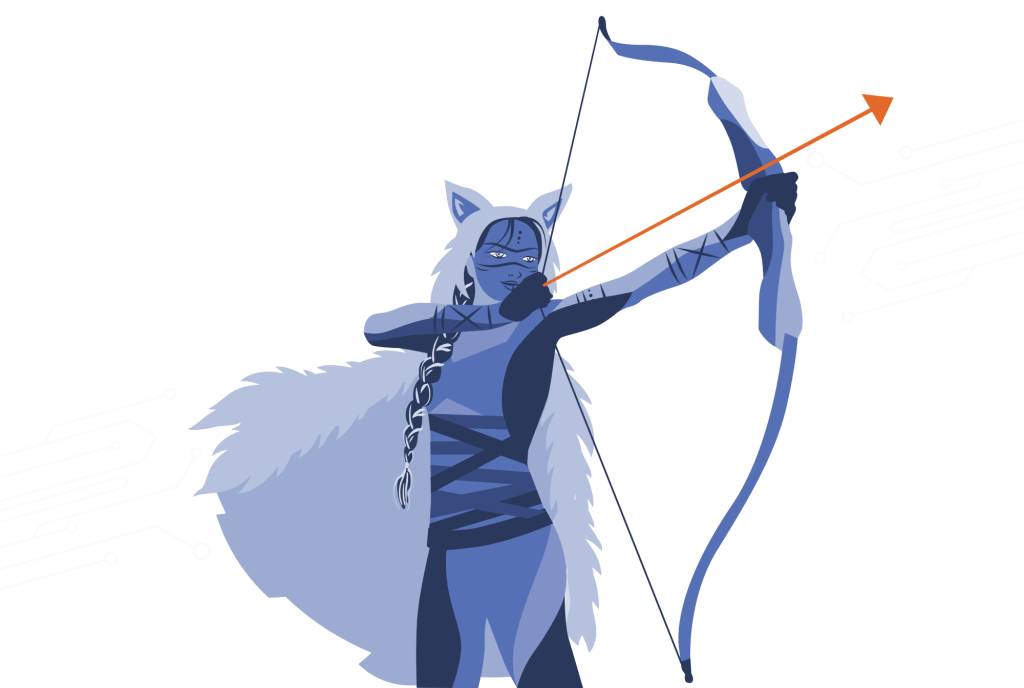
AUTONOMOUS CYBERSECURITY · POWERED BY FROSTBOW™⟶
Attackers Operate at Machine Speed So Does FrostbowTM.
Frostbow™ is SKADI’s AI-powered autonomous security platform that ingests, analyzes, and resolves security alerts without human intervention—eliminating alert queues, after-hours gaps, and analyst burnout.
Powered by ontological AI, Frostbow™ makes autonomous decisions 99.6% of the time.
- No alert queues.
- No overnight gaps.
- No security analyst burnout.
Enterprise-grade cyber defense, without the enterprise cost.